In a world where data breaches lurk around every digital corner and cyber attackers play a relentless game of cat and mouse, the dark web has become a notorious hub for illicit activities. But fear not, dear reader, for we are about to embark on a journey through the twists and turns of the dark web, shedding light on the enigmatic concept of a dark web scan. So, kick back, relax, and let’s unravel the mysteries together.

🌐 What is the Dark Web?
Before we delve into the intricacies of dark web scans, let’s demystify the dark web itself. It’s like the clandestine underbelly of the internet—a network of sites hidden within darknets. Picture it as a secret club that requires a special browser, Tor, to gain entry. While some legitimate corners exist, the dark web is often associated with notorious marketplaces, reminiscent of the infamous Silk Road.
🔄 How Can Your Info End Up There?
Now that we know what the dark web is, the burning question arises: how can your personal information end up in this digital underworld? Hacking, my friend. Hackers seek your credit card numbers, social security details, and more through methods like malware or phishing scams. Large-scale data breaches also play a role, with stolen data finding its way into the dark web marketplace.
🔍 What Exactly is a Dark Web Scan?
Enter the hero of our story—the dark web scan. This online security tool is your digital guardian, scouring the dark web for traces of your personal information among stolen data lists. It’s like having a cyber detective constantly on the lookout for any signs of foul play involving your sensitive details.
🚀 How Does a Dark Web Scan Work?
Equipped with specialized software, a dark web scan navigates the non-indexed corners of the dark web, employing algorithms to hunt for your name, email, social security number, and credit card details in data dumps. Should it find anything amiss, you’re promptly alerted, empowering you to take swift action and fortify your digital defenses.
👀 What Do Dark Web Scanners Seek?
Dark web scanners aren’t just snooping around for kicks; they’re on a mission to uncover and report illegal activities. From stolen data to illicit substances and even terrorist content, these scanners act as the virtual sheriffs patrolling the dark web’s virtual streets.
How Can You Scan the Dark Web for Free?
Now, the thrifty among us may be wondering: can we keep our wallets intact while safeguarding our digital identities? Fear not! We’ve unearthed a few free tools for a quick dark web scan. Firefox Monitor, MyPwd, IDStrong, and Have I Been Pwned offer varying degrees of protection, helping you keep an eye on your digital backdoor without breaking the bank.
🚨 What to Do If Your Info is Detected?
Discovering your information in the dark web’s shadows can be unsettling, but fear not. We’ve compiled a handy guide: change passwords, notify financial providers, monitor statements, order credit reports, freeze credit, check app permissions, and be cautious with your data sharing. With these steps, you’ll be the digital Sherlock Holmes of your own online security.
🌐 Limitations of Dark Web Scanning
Like any good detective, dark web scanners have their limitations. They can’t cover the entire dark web, and if they find something, your data might already be in the wrong hands. But hey, knowing is half the battle, and armed with information, you can take proactive steps to shield yourself.
✔️ Verdict: Is a Dark Web Scan Worth It?
Now, the million-dollar question: should you invest in a dark web scan? It all boils down to your risk level and personal circumstances. High-risk individuals may find it a worthy investment, but everyone should approach dark web scan services with a healthy dose of skepticism. The best defense is still vigilance and proactive steps to fortify your digital fortress.
Webwasher proxy.Pac
A Webwasher proxy.Pac, often referred to as a Proxy Auto-Configuration file, is a script utilized by web browsers to automatically configure proxy settings. This configuration file helps manage web traffic, directing it through a proxy server. These files are commonly used for network security and content filtering.
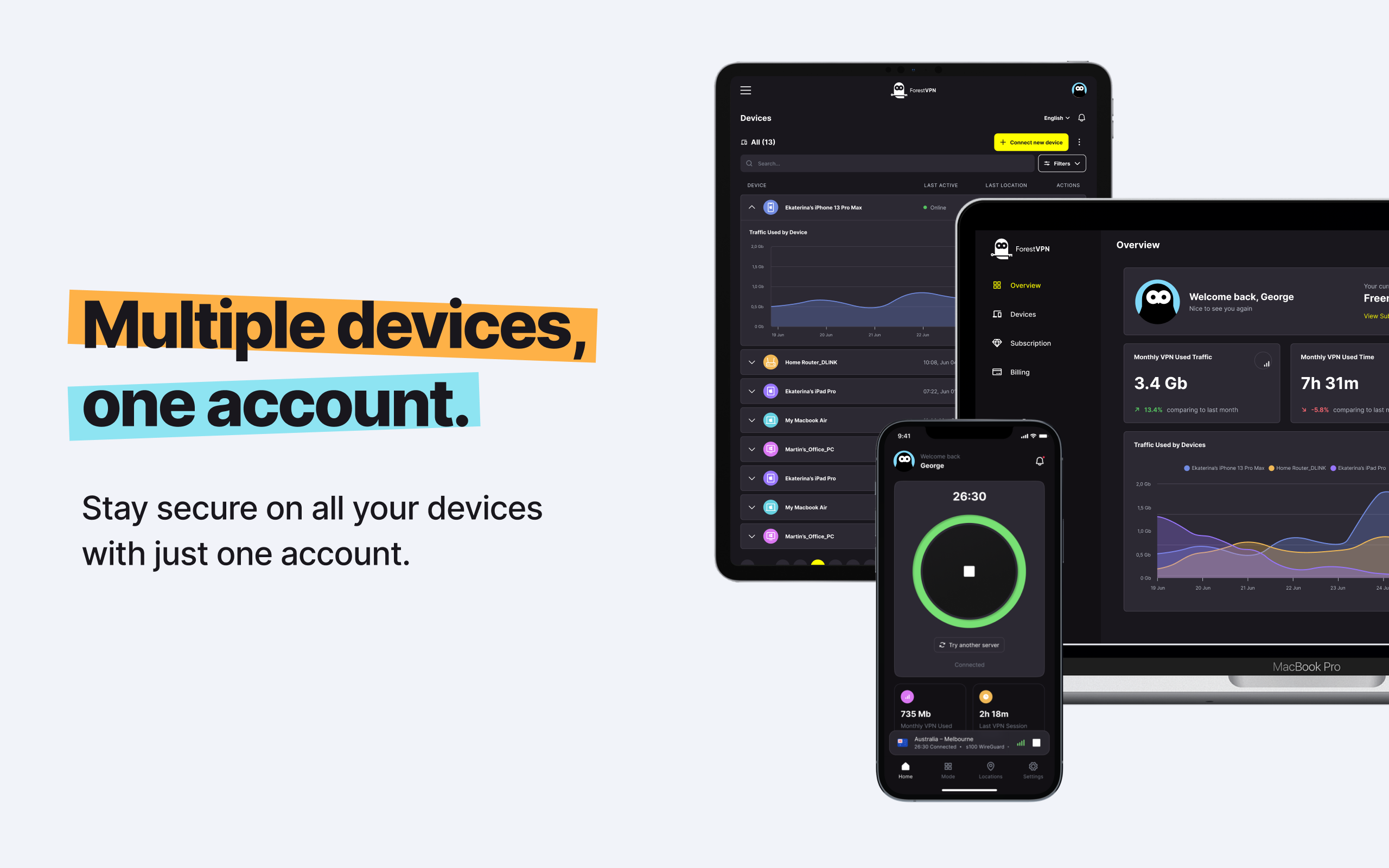
In simpler terms, think of it as a traffic cop for your internet data, guiding it through a specific route for enhanced security. Now, if you’re looking to safeguard your online journey, consider exploring ForestVPN. It’s not just a VPN; it’s your digital bodyguard, ensuring your internet travels are safe and secure. Learn more at ForestVPN.