In the vast expanse of the internet, where information flows freely and connections are made with a click, lies a dark underbelly of cyber threats. Your digital persona, built on usernames, passwords, and personal details, can become vulnerable prey to online stalkers and doxing—an unsettling practice where private information is weaponized against you. But fear not, for we’re here to shed light on this shadowy realm and arm you with the knowledge to defend yourself against online stalkers and doxing

What is Doxing?
Doxing, derived from “dropping documents,” is the sinister act of exposing personal information about someone without their consent. This information, once unleashed into the digital wild, can be exploited in myriad ways, from harassment and cyberbullying to identity theft and physical threats. Your home address, phone number, workplace details, and even sensitive data like passport or credit card numbers—all fair game in the eyes of a doxer.
Why Do People Dox Others?
Doxing often emerges as a tool of retaliation or intimidation. It’s the online equivalent of throwing stones from the safety of anonymity. Whether it’s disagreements, personal vendettas, or ideological clashes, anyone can fall victim to the crosshairs of a determined doxer. From high-profile personalities to everyday individuals, no one is immune to the perils of online harassment.
How Do Doxers Operate
Doxers, equipped with digital sleuthing skills, scour the internet for breadcrumbs of your existence. Public records, social media posts, and even innocuous details like your favorite coffee shop can paint a vivid portrait of your life. Armed with this information, doxers piece together the puzzle of your identity, exposing vulnerabilities you never knew existed.
Common Sources of Information for Doxers:
- Public records: Voter registrations, property ownership, and court documents.
- Social media oversharing: From geo-tagged selfies to innocuous status updates.
- IP tracing: Your online activities can inadvertently reveal crucial details about your whereabouts.
Is Doxing Illegal?
While the moral compass may condemn doxing as unethical, legality often paints a different picture. Much of the information doxers unearth resides in the public domain, blurring the lines between privacy rights and digital transparency. However, crossing into the realm of illegal activity—such as divulging private financial information—carries severe consequences, both legal and ethical.
Strategies Against Doxing
Armed with knowledge and vigilance, you can fortify your online defenses against the specter of doxing. Here are actionable steps to safeguard your digital sovereignty:
1. Embrace Anonymity:
Separate your online persona from your real-world identity. Utilize pseudonyms and random username generators to obfuscate your digital footprint.
2. Monitor Your Digital Trail:
Regularly scour the internet for mentions of your name and personal details. Stay informed about what information lurks in the shadows of cyberspace.
3. Fortify Your Privacy Settings:
From social media platforms to search engines, tweak your privacy settings to minimize exposure to prying eyes.
4. Strengthen Password Security:
Ditch the predictable passwords and opt for robust combinations of characters, numbers, and symbols. Consider employing a password manager for added security.
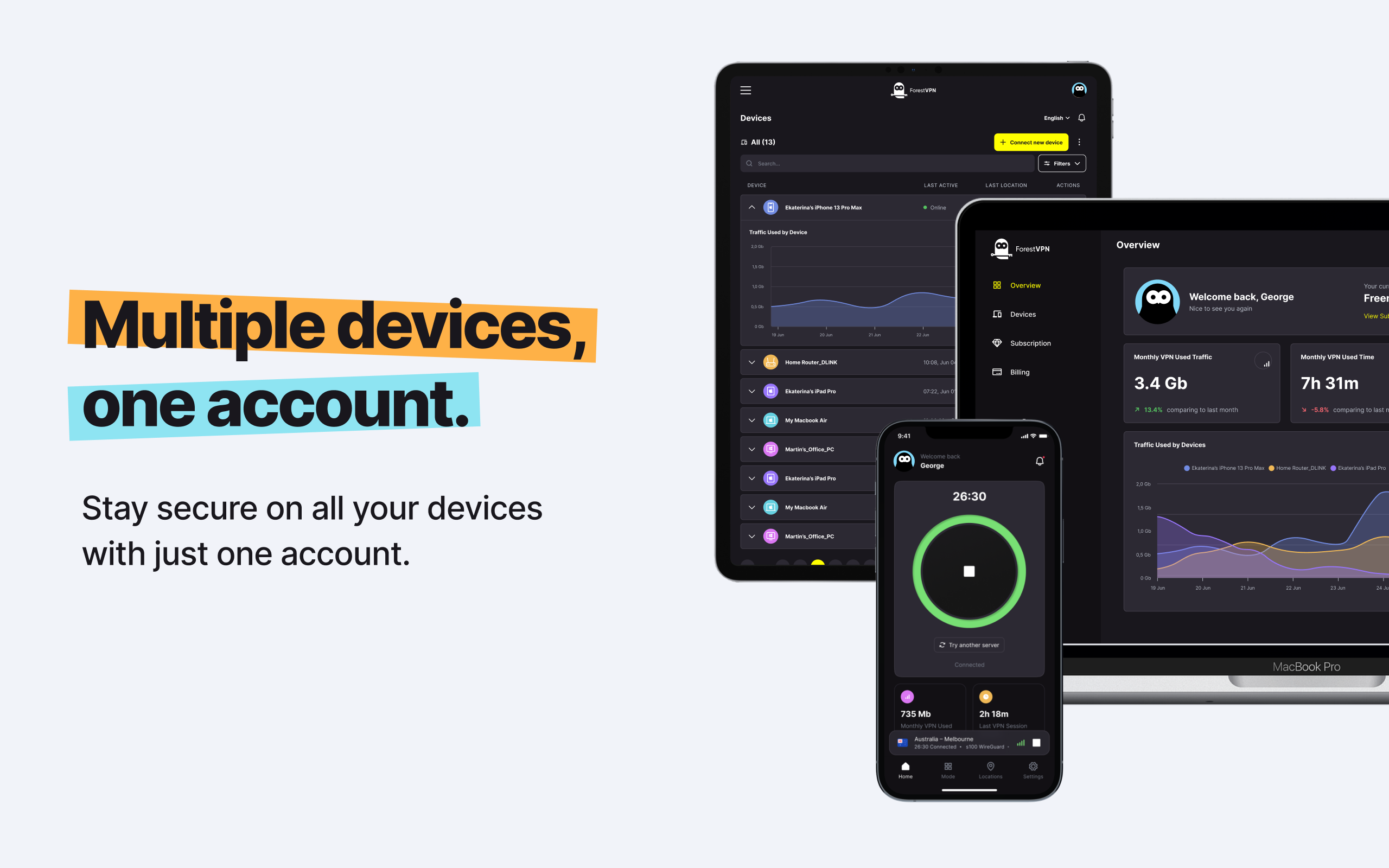
5. Harness the Power of VPNs:
VPN cloak your online activities, shielding your digital whereabouts from prying eyes. With ForestVPN, you can navigate the digital wilderness with confidence and anonymity.
Vpn local device name already in use
When encountering the error message “Vpn local device name already in use,” it typically indicates a conflict within the network settings, where the VPN adapter’s device name clashes with an existing network resource. To resolve this issue, you can try the following steps:
- Restart your device: Sometimes, a simple reboot can clear out temporary network glitches and resolve conflicts.
- Release and renew IP addresses: Use the command prompt to release and renew IP addresses, which can help refresh network configurations.
- Check network adapter settings: Ensure that your VPN adapter settings don’t overlap with existing network resources. You can modify the device name or IP address to avoid conflicts.
- Update VPN software: Make sure you’re using the latest version of ForestVPN or any other VPN software to benefit from bug fixes and compatibility improvements.
Remember, addressing network conflicts requires patience and technical know-how. By following these steps and leveraging ForestVPN’s robust features, you can enjoy seamless and secure online experiences without encountering device name conflicts.
For further assistance and to explore ForestVPN’s comprehensive suite of privacy and security solutions, visit ForestVPN today!