In the vast realm of cybersecurity, the Point-to-Point Tunneling Protocol (PPTP) has had its fair share of the limelight. Despite its historical significance, PPTP now resides in the shadows, deemed obsolete and riddled with security vulnerabilities. However, its journey and intricacies unveil a narrative worth deciphering.
Unraveling the Concept of VPN Protocols
Before delving into the intricacies of PPTP, let’s decipher the essence of VPN protocols. These protocols serve as the backbone, orchestrating secure connections between your device and the VPN server. They encapsulate authentication, confidentiality, and integrity, forming the pillars of a secure VPN experience.
The Fundamental Attributes of a VPN Protocol
A robust VPN protocol should possess three indispensable attributes:
- Authentication: Safeguarding against unauthorized access.
- Confidentiality: Encrypting data to thwart interception.
- Integrity: Detecting and preventing data tampering.
Today’s VPN landscape boasts a plethora of protocols, including PPTP, L2TP/IPsec, OpenVPN, and the revolutionary WireGuard®.

Decoding the Genesis of PPTP VPN
An Ode to History
Conceived by a consortium led by Microsoft, PPTP saw the light of day in 1999. It swiftly ingrained itself into the fabric of corporate networks, owing to its compatibility and simplicity.
The Ecosystem of Support
Over two decades, PPTP garnered native support across diverse platforms, from Windows 95 to modern Linux distributions. However, the tides turned against it as Apple bid adieu to PPTP support in iOS 10+ and macOS 10.12 Sierra, signaling a shift towards more secure alternatives.
Under the Hood: How PPTP Functions

PPTP operates as a tunneling protocol, leveraging the Point-to-Point Protocol (PPP) for encryption and authentication. By establishing a TCP connection to the VPN server and encapsulating packets using GRE, PPTP navigates the digital realm with finesse.
Performance and Security: A Balancing Act
Speed and Simplicity
Brimming with simplicity, PPTP boasts commendable speed, ideal for devices with modest processing capabilities. Its lightweight nature ensures optimal performance, making it a contender in the VPN arena.
Security Concerns
Yet, beneath the veneer of convenience lurk critical security flaws. From un-encapsulated authentication exploits to susceptibility to bit-flipping attacks, PPTP exposes users to an array of vulnerabilities. The revelations from Edward Snowden’s leaks only exacerbated the skepticism surrounding its security posture.
The Verdict: PPTP in Contemporary Context

In essence, PPTP stands as a relic of a bygone era, marred by security pitfalls. While it may find utility in specific scenarios devoid of security exigencies, its obsolescence is irrefutable.
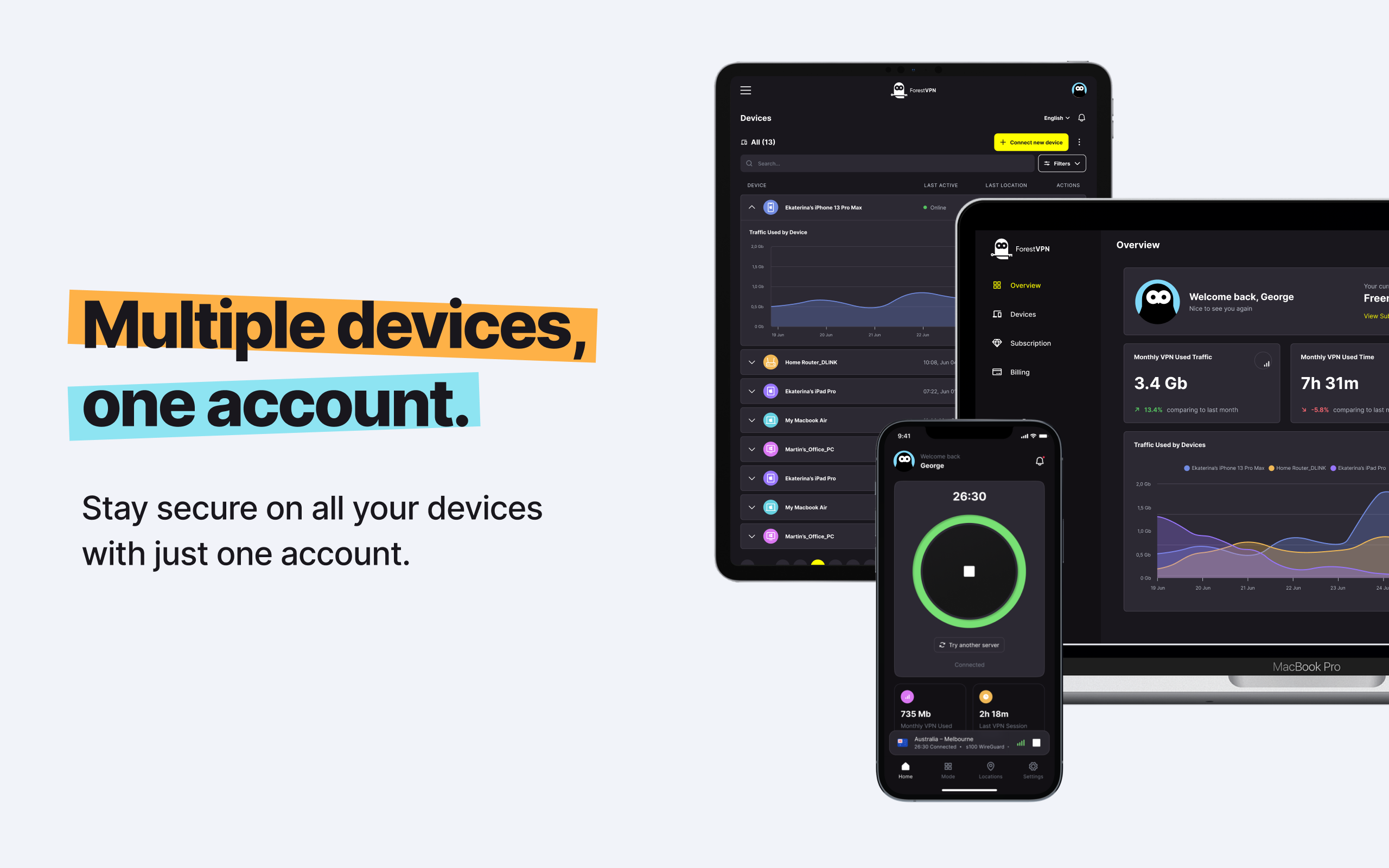
At ForestVPN, we advocate for uncompromising security. Our arsenal comprises cryptographically secure protocols like OpenVPN, IKEv2, and WireGuard. We prioritize your digital well-being above all else.
Frequently Asked Questions
1. What port does PPTP use?
PPTP operates through TCP port 1723.
2. What is PPTP passthrough?
A PPTP passthrough facilitates seamless routing of PPTP traffic through routers, ensuring uninterrupted connectivity.
3. Do I need a PPTP client?
Most modern devices include native PPTP clients, except for Apple devices, which have phased out support for this protocol.
4. How does PPTP compare to modern VPN protocols?
PPTP pales in comparison to modern protocols like OpenVPN and WireGuard in terms of security and reliability.
5. Is PPTP resistant to censorship?
Unfortunately, PPTP is susceptible to censorship due to its predictable port and encapsulation methods.
Answer to “Vpn gateway aws”:
In the realm of cloud networking, AWS offers the Virtual Private Network (VPN) Gateway service, facilitating secure connections between your on-premises network and AWS cloud resources. This gateway acts as a conduit, ensuring data confidentiality and integrity across the network infrastructure.
To establish a VPN gateway in AWS, you navigate through the AWS Management Console, configuring VPN connections and customer gateways. Leveraging ForestVPN, you can fortify your AWS infrastructure with state-of-the-art encryption and protocol standards, ensuring a resilient shield against cyber threats.
For detailed guidance on setting up a VPN gateway in AWS and fortifying your digital fortress, visit our comprehensive documentation at ForestVPN.