In the vast realm of digital communication, where privacy is a luxury, Pretty Good Privacy (PGP) emerges as the knight in shining armor. Developed by Phil Zimmermann in 1991 and later released as OpenPGP in 1997, this encryption marvel allows users to safeguard their texts, files, emails, or even entire disks. Join us on this journey as we delve into the history, mechanics, setup, and nuances of PGP.
Unveiling the History of PGP
Phil Zimmermann, a fervent anti-nuclear activist in the ’80s and ’90s, birthed PGP with the intention of securing files beyond government intrusion. Despite encryption being classified as military munition back then, Zimmermann defiantly distributed PGP’s source code globally, backed by the First Amendment. His resilience paid off when all accusations against him were dropped in 1996, marking a significant triumph.
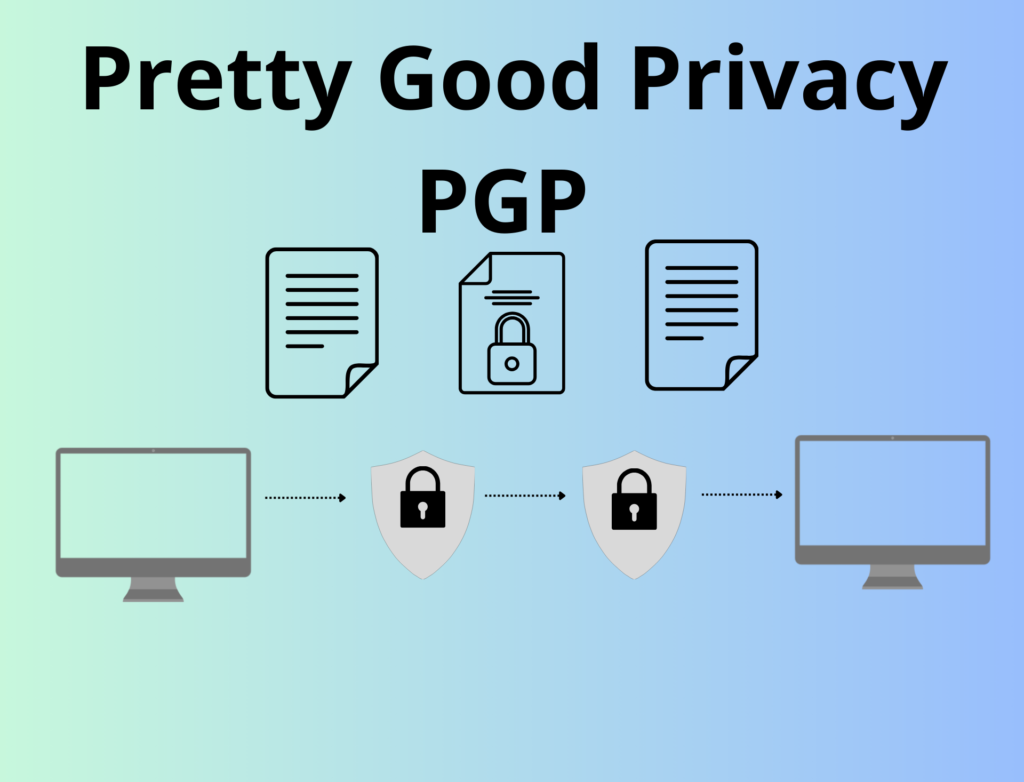
How Does it Work?
PGP operates as a pseudonymous system, ensuring the privacy of data and authenticating communication. While it enhances anonymity in conjunction with tools like Tor, it can also be used to digitally sign statements or reviewed files, revealing the author’s identity. Understanding PGP involves creating a public and private key pair, where the public key is shared openly, and the private key remains securely on the user’s device.
Navigating the Web of Trust
PGP tackles the challenge of authenticating public keys through the “web of trust.” Users sign each other’s keys, creating a chain of trust. However, this process can be intricate and revealing, limiting its widespread adoption.
Setting Up PGP on Your Device
To embark on the PGP journey, users need to choose a program suitable for their device. From GPGTools on macOS to Guardian Project on Android, diverse options cater to different needs. Key creation, backup strategies, and setting expiration dates are vital steps to ensure a secure experience.
Sending Encrypted Messages with PGP
Before diving into encrypted messages, obtaining the public keys of your contacts is paramount. Uploading your PGP key to public servers or personal platforms enhances visibility. PGP’s versatility allows users to encrypt files effortlessly, providing a secure means of communication.
Limitations and Best Practices
While PGP’s mathematical foundation is robust, potential exploits exist, primarily in authenticating public keys. It does not encrypt metadata, and a compromised key can expose historical communications. Regular key updates, strong passwords, and cautious metadata sharing are pivotal for PGP users.
ForestVPN: A Glimpse into the Future
In the ever-evolving landscape of online security, ForestVPN emerges as a beacon of protection. Offering encrypted connections and secure browsing, ForestVPN aligns with the principles of user privacy. As we navigate the digital forests, let ForestVPN be your companion in the quest for a secure online experience.
FAQ
Q: How does PGP ensure the authenticity of communication?
A: PGP achieves communication authenticity through digital signatures. When you sign a file or statement using your private key, it serves as a cryptographic proof of your authorship, adding an extra layer of trust to your communication. ForestVPN, with a commitment to user privacy, follows similar principles in securing your online presence.
Q: Can PGP protect metadata, and how does ForestVPN address this concern?
A: PGP focuses on encrypting content, not metadata. ForestVPN, with its advanced encryption protocols, safeguards not only your content but also protects metadata associated with your online activities, ensuring comprehensive privacy.
Q: What makes ForestVPN a reliable alternative to PGP for online security?
A: ForestVPN offers encrypted connections, secure browsing, and robust privacy features, making it an excellent choice for those seeking a comprehensive and user-friendly online security solution. With ForestVPN, step into a secure digital realm where your privacy is a top priority.

