In the modern workplace, more than half of employees globally opt to bring their personal devices to work. This trend, commonly known as Bring Your Own Device (BYOD), reflects a shift in how we interact with technology. While the concept holds promises of flexibility and convenience, it also raises concerns regarding data security and network integrity.
The Real Risks of BYOD: Navigating the Wild West
Diverse Devices, Diverse Risks
The allure of BYOD lies in its flexibility, but it comes with a caveat: the influx of foreign devices brings a myriad of risks. Each device boasts its unique operating system, network settings, and user controls. Despite the ideal scenario of users promptly updating patches and securing their devices, reality often paints a different picture. In many organizations, IT departments find themselves grappling with a diverse array of devices, ranging from the latest models to aging gadgets. This diversity fosters a “Wild West” environment where standardization becomes elusive, and security concerns loom large.
Cloud Services: A Double-Edged Sword
David Cripps, Chief Security Officer of Investec, highlights a significant risk associated with BYOD adoption: the proliferation of cloud services. While companies may endorse a handful of official cloud services vetted by IT professionals, the actual landscape often reveals a different story. BYOD users gravitate towards their preferred applications and services, regardless of official endorsements. Unfortunately, many of these services lack fundamental security measures, leaving corporate networks vulnerable to data breaches and compromises. The democratization of technology further exacerbates the situation, blurring the line between convenience and security.
The IoT Conundrum
The evolution of the Internet of Things (IoT) introduces a new layer of complexity to the BYOD landscape. With IoT devices gaining prominence, organizations face the challenge of securing a diverse range of endpoints, each with its unique access privileges. Recent incidents, such as the Backoff POS malware, underscore the vulnerabilities inherent in IoT devices. As IoT permeates various aspects of corporate infrastructure, robust security measures become imperative to safeguard sensitive data and critical functions.
Best Practices for BYOD Management: Navigating the Minefield

Embrace Shadow IT
Rather than viewing Shadow IT as a hindrance, organizations should encourage transparency and collaboration. By embracing Shadow IT, companies gain insights into user preferences and behaviors, allowing them to implement targeted security measures effectively. Transparency fosters a culture of accountability, empowering employees to make informed decisions while mitigating potential risks.
Network Protection and Vigilance
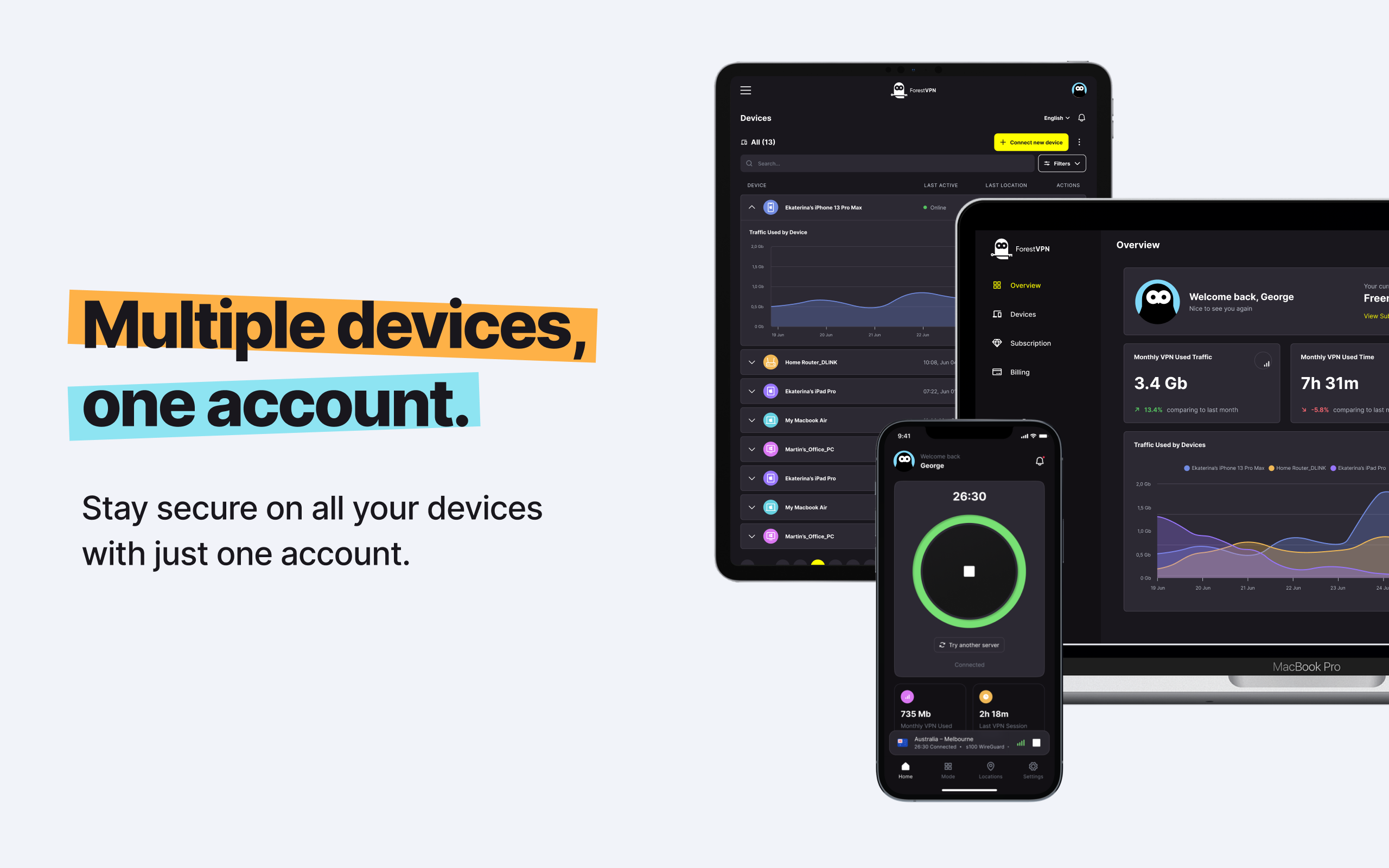
Protecting the network requires a multi-faceted approach that encompasses both proactive measures and vigilant monitoring. Implementing comprehensive network security protocols, including robust firewalls and intrusion detection systems, forms the cornerstone of effective network protection. Additionally, leveraging secure VPN services, such as ForestVPN, helps obscure network traffic, minimizing the risk of unauthorized access and data breaches.
Conclusion: Navigating the BYOD Terrain

In conclusion, the adoption of BYOD presents both opportunities and challenges for modern enterprises. While the allure of flexibility and productivity gains is undeniable, the inherent risks demand careful consideration and proactive mitigation strategies. By implementing best practices and embracing emerging technologies, organizations can navigate the BYOD terrain with confidence, safeguarding their data and maintaining network integrity.
FAQs: Answering Your Burning Questions
- Is BYOD inherently risky?
- BYOD introduces inherent risks due to the diversity of devices and the proliferation of cloud services. However, with robust security measures in place, organizations can mitigate these risks effectively.
- What steps can organizations take to secure BYOD environments?
- Organizations can develop comprehensive use policies, provide ongoing support for all devices, and encourage transparency regarding Shadow IT.
- Why is network protection crucial in the context of BYOD?
- Network protection is essential to safeguard sensitive data and critical functions from unauthorized access and breaches. Secure VPN services, such as ForestVPN, play a pivotal role in obscuring network traffic and bolstering overall security.
- How can employees contribute to a secure BYOD environment?
- Employees can adhere to organizational policies, stay vigilant against potential threats, and report any security concerns promptly to the IT department.
- What role does emerging technology, such as IoT, play in BYOD security?
- The proliferation of IoT devices introduces new challenges to BYOD security, emphasizing the need for adaptive security measures and proactive risk management strategies.
Answer to Gateway to Gateway VPN:
Gateway to gateway VPN, also known as site-to-site VPN, establishes secure connections between two or more networks over the internet. It enables seamless communication and data exchange while maintaining confidentiality and integrity.
To set up a gateway to gateway VPN, organizations deploy compatible VPN gateways at each network’s perimeter. These gateways authenticate and encrypt traffic flowing between the networks, ensuring secure transmission across the internet.
ForestVPN offers robust gateway to gateway VPN solutions tailored to meet diverse organizational needs. With our secure and reliable VPN services, organizations can establish encrypted connections between geographically dispersed locations, safeguarding sensitive data and maintaining network integrity. Explore ForestVPN today to fortify your network infrastructure and elevate your security posture. Learn more.