You might be using ciphertext more often than you think. It’s like a secret code that protects your digital conversations from prying eyes. Let’s delve into what ciphertext is, why it’s essential, and how it safeguards your online activities.
Unveiling Ciphertext
Ciphertext isn’t as complex as it sounds. It’s simply encrypted text, the result of scrambling plain text using algorithms. It’s like turning a sentence into a puzzle that only the intended recipient can decipher.
Imagine this article encrypted. Instead of readable sentences, you’d see a jumble of characters. That’s ciphertext for you! It’s like baking a cake: encryption is the recipe, and ciphertext is the delicious outcome.
The Power of Encryption
Why Encrypt? Well, imagine sending a postcard through the mail. Anyone who intercepts it can read your message. But if you put it in a locked box (encryption), only the person with the key (decryption key) can unlock it.
Online, data travels like invisible postcards. Without encryption, it’s an open invitation for hackers to peek at your sensitive information—like online banking credentials.
Decrypting Decryption Keys
Encryption relies on keys—rules that computers follow to encode and decode data. Think of it as a lock and key system. There’s a public key for encoding and a private key for decoding. It’s like sending a package; only the recipient has the right key to open it.
Exploring Cipher Types
There are two main types of ciphers: block and stream ciphers.
- Block Ciphers: These encrypt data in fixed-size blocks, ensuring robust security. AES, DES, and 3DES are common examples used by corporations and VPNs like ForestVPN.
- Stream Ciphers: They encrypt data in continuous streams, offering speed but sacrificing some security. Think of them as swiftly flowing rivers of encoded data.
Crack the Code: Ciphertext Attacks
Hackers have two main strategies to break encryption: cryptanalysis and brute-force attacks.
- Cryptanalysis: It’s like finding weaknesses in a fortress. Hackers search for flaws in encryption algorithms to decipher the ciphertext.
- Brute-force Attacks: Imagine trying every key in the universe to unlock a door. It’s possible but incredibly time-consuming. For instance, cracking 256-bit encryption would take longer than the age of the universe!

Why Encrypt? For Your Digital Armor
Encrypting your data with ciphertext is like putting on armor before a battle. It shields your sensitive information from cyber threats lurking in the digital realm.
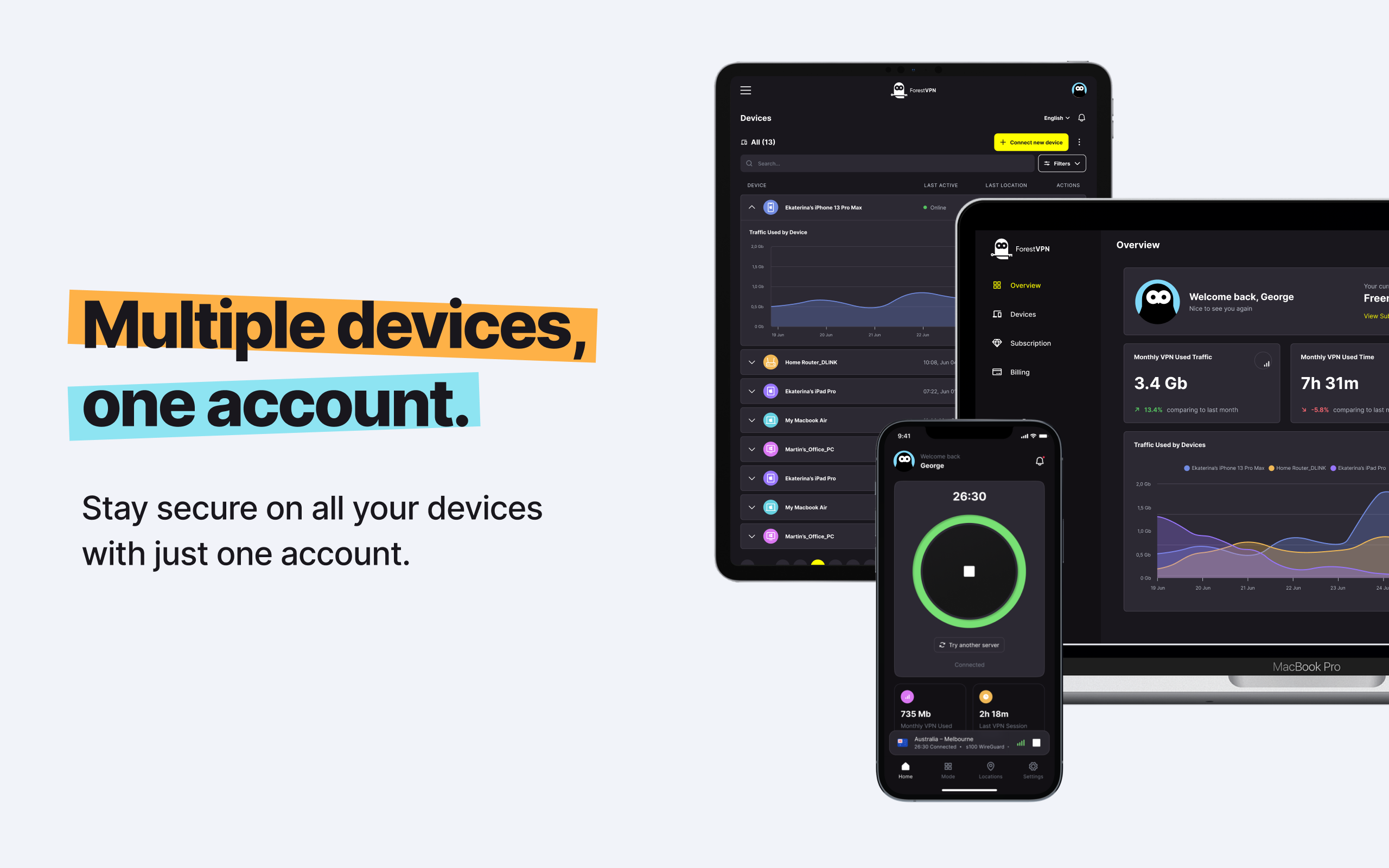
Using ForestVPN offers enhanced encryption, ensuring your online activities remain private and secure, no matter where you connect from. With a vast network of servers worldwide, ForestVPN provides the shield you need for safe browsing.
Summary
In a nutshell, ciphertext is your digital cloak of invisibility, shielding your online activities from prying eyes. By encrypting your data with ForestVPN, you’re ensuring robust protection against cyber threats and maintaining your privacy in the vast expanse of the internet.
FAQs (Frequently Asked Questions)
- Is ciphertext the same as encryption?
- No, ciphertext is the result of encryption. It’s like the secret code that hides your message.
- How secure is ciphertext?
- Ciphertext offers robust security, especially when coupled with advanced encryption algorithms like AES.
- Can ciphertext be decrypted without the key?
- Decrypting ciphertext without the proper key is nearly impossible, thanks to the complexity of modern encryption algorithms.
- Why should I use encryption for my online activities?
- Encryption safeguards your sensitive information, such as passwords and financial data, from cyber threats and unauthorized access.
- How does ForestVPN enhance encryption?
- ForestVPN employs cutting-edge encryption protocols and a vast network of secure servers worldwide, ensuring your online activities remain private and protected.