In the vast, interconnected web of the internet, cyber threats lurk like silent ninjas, ready to pounce on unsuspecting users. One such ninja move is the infamous replay attack—a cunning maneuver where a cyber assailant intercepts and replays secure data transmissions, effortlessly slipping into the digital shadows.

Understanding the Sneaky Dance: How Replay Attacks Work
Imagine Tom sending a simple login request to a website. The website validates the request, and Tom gains access. But here comes Sally, the digital trickster. She intercepts the login request, doesn’t bother decrypting it, and smoothly replays it. Voila! The website, none the wiser, believes Tom is logging in again, granting access to Sally in Tom’s disguise.
Packet Sniffing: Eavesdropping in the Digital Realm
Hackers, much like spies of the cyber world, engage in packet sniffing—an act of eavesdropping on data exchanges through networks. Once intercepted, they replay the pilfered data, often targeting sensitive information like usernames, passwords, or coaxing users into unwittingly funding their cyber escapades.
The Illusion of Encryption: Pass-the-Hash Attack
You might think encrypted passwords are the fortress against replay attacks. Think again. Even if passwords are hashed (scrambled using a secret key), a successful authentication opens the door for hackers. They don’t need your password; they just need to replay the authentication—a sinister game called “pass-the-hash attack.”
Adding Spice to Security: Hashing and Salting Passwords
To add a dash of security flavor, passwords undergo the “hashing and salting” process. Salting involves adding a unique string of characters to each password. But beware, not all sites are culinary experts; some reuse the same salt, leaving your security less savory.
The Counterattack: One-Time Passwords and Timestamps
If a secure, encrypted password falls short, we pull out the big guns—One-Time Passwords (OTPs) and timestamps. OTPs are a one-shot deal, and timestamps limit a hacker’s window of opportunity. It’s like handing them a Rubik’s Cube with missing pieces.
The Armor of the Internet: HTTPS and VPNs
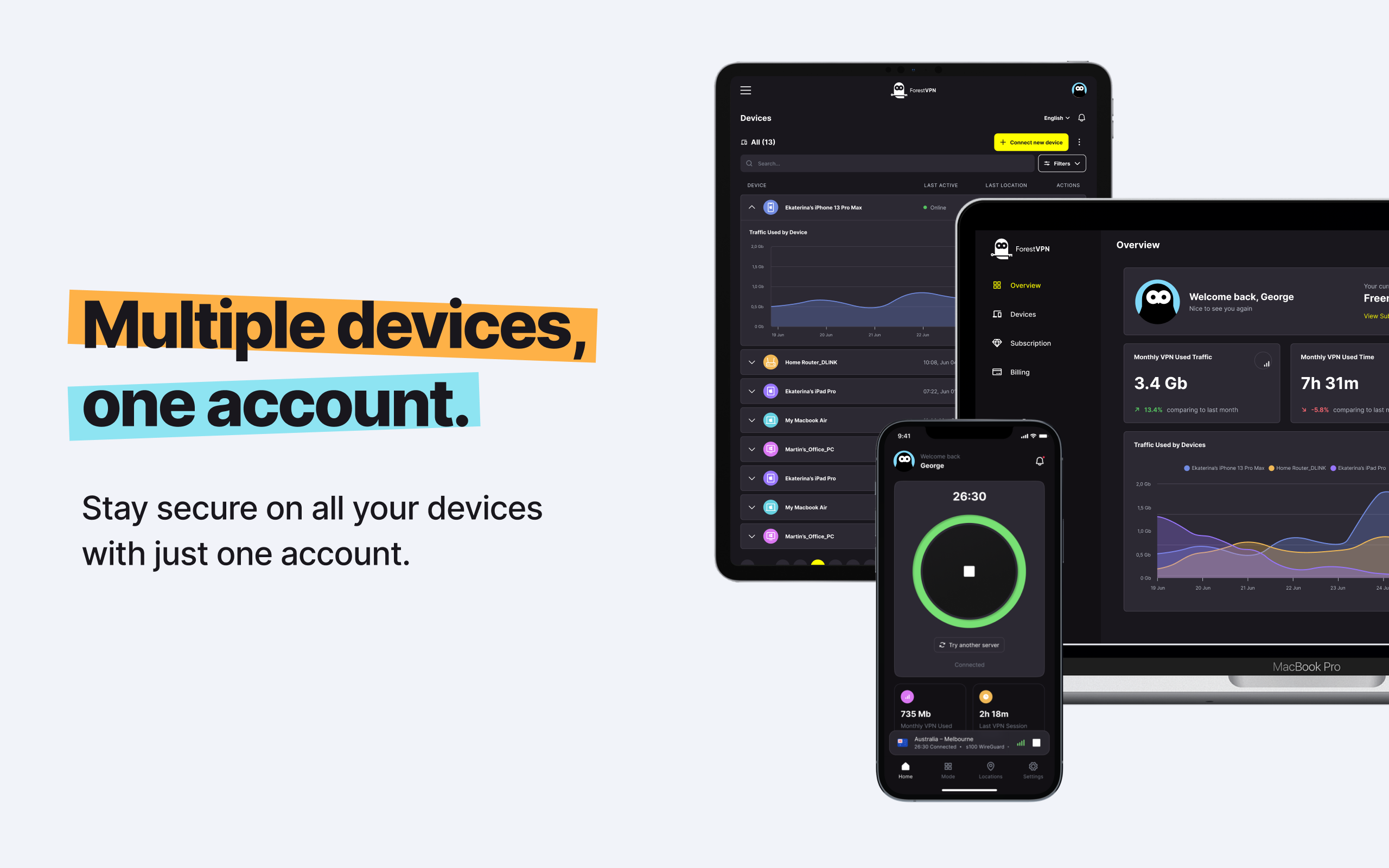
Entering the battlefield of the internet? Arm yourself with HTTPS-enabled websites and steer clear of public Wi-Fi battlegrounds. However, the pièce de résistance is a Virtual Private Network (VPN) that not only masks your internet traffic but kicks potential eavesdroppers to the digital curb.
FAQ
1. How common are replay attacks?
Replay attacks are surprisingly common in the digital realm. Cyber tricksters are always on the lookout for vulnerabilities to exploit.
2. Can encrypted passwords prevent replay attacks?
While passwords are often encrypted, a successful authentication opens the door for replay attacks. It’s like having a locked door but leaving the key under the mat.
3. What’s the role of salting in password security?
Salting adds a unique flavor to password security by introducing a secret ingredient. However, some websites serve the same recipe to every dish, compromising security.
4. Why use a VPN to prevent replay attacks?
A VPN acts like a digital invisibility cloak, keeping your internet traffic hidden from prying eyes and potential replay attackers.
5. Are replay attacks preventable, or are they inevitable?
While no defense is foolproof, implementing strong password practices, OTPs, and VPNs significantly reduces the risk of falling victim to replay attacks.
Httpwebrequest proxy pac
In the vast realm of Httpwebrequest proxy pac, we find ourselves navigating a maze of technical intricacies. Httpwebrequest is a class in .NET used to send HTTP requests to a URL. When it comes to proxy pac, it’s all about Proxy Auto-Configuration—a file that simplifies the configuration of web browsers’ proxy settings.
So, what’s the scoop with Httpwebrequest proxy pac? It’s like having a personal chauffeur for your internet travels. Proxy Auto-Configuration (PAC) scripts, often ending with a .pac extension, dictate how your browser should route traffic through various proxies.
But why should we care about Proxy PAC with ForestVPN?
Well, ForestVPN takes your online journey to the next level. Imagine Proxy PAC as a trusty map, and ForestVPN as your secret shortcut through the digital woods. By seamlessly integrating with Proxy Auto-Configuration, ForestVPN ensures your internet traffic takes the scenic, secure route, dodging cyber threats like a nimble forest creature.
So, if you’re venturing into the wilderness of Httpwebrequest proxy pac, let ForestVPN be your guide. Navigate the digital trails with confidence and security. Check out ForestVPN for the ultimate cybersecurity companion.